Why Ecommerce Needs AI Breach Training
AI breach training equips ecommerce teams to detect AI-powered phishing, cut detection time, reduce fraud losses, and maintain compliance with adaptive simulations.

Ecommerce faces a growing cybersecurity crisis. By 2026, over 65% of online retailers are expected to experience major data breaches, with global fraud losses projected to exceed hundreds of billions annually. Cybercriminals are increasingly using AI to exploit vulnerabilities, while outdated security measures and training leave businesses exposed.
Here’s why AI-based breach training is the solution:
- AI-driven threats dominate: 80% of phishing attacks now use AI, bypassing traditional defenses.
- Outdated methods fail: Static, infrequent training can't keep up with evolving attacks.
- AI breach training works: Businesses with AI-powered systems see faster threat detection, reduced fraud losses, and better compliance with regulations like PCI DSS 4.0.
AI breach training equips ecommerce teams to combat sophisticated threats, reduce detection times, and protect customer trust. With rising fraud costs and stricter regulations, adopting AI-driven security measures is no longer optional - it’s essential for survival.
Cybersecurity Masterclass: How AI is Redefining Cyber Defense
Why Traditional Breach Training Falls Short
Ecommerce security training is stuck in the past, designed to handle predictable threats instead of the constantly shifting, sophisticated attacks businesses face today.
Outdated and Infrequent Training Methods
Most traditional breach training happens just once or twice a year, often in the form of generic, one-size-fits-all sessions. This approach leaves employees ill-prepared, as evidenced by a 30–40% click rate on phishing emails among those without proper training.
Hoxhunt highlights the core issue:
"Awareness-based training doesn't reduce risk. To reducing risk, you need to change your employees habits."
The problem is that these sessions rely on outdated, repetitive templates that fail to keep up with the rapid evolution of cyber threats. For instance, between January 2021 and May 2022, phishing attacks surged by 250%, yet many programs still rely on old examples. Worse, they often focus solely on email-based threats, ignoring newer tactics like SMS phishing, voice phishing, and even deepfake attacks. This outdated approach not only leaves employees vulnerable but also slows down the detection of threats.
False Alarms and Delayed Responses
Another major flaw lies in the reactive nature of traditional tools, which depend on signature updates or manual analysis. This creates a dangerous lag, with the average detection window stretching to 207 days. Adrian Luna from Webscale explains:
"Traditional security tools operate on a delay. Firewalls are typically reactive instead of proactive, totally dependent on signature updates or analyst intervention."
During this delay, attackers have ample time to infiltrate systems, learn operational workflows, and plan their attacks. Compounding this issue is the reliance on rigid, rule-based logic - such as "if X happens, do Y" - which falls short against modern threats. Many of these threats use AI-driven methods to bypass traditional defenses, blending seamlessly into normal system traffic. This leaves security teams scrambling to catch up, often too late.
Failure to Address New Attack Methods
Traditional training also fails to prepare teams for the latest wave of adaptive, AI-driven threats. Up to 80% of phishing attacks now leverage AI, creating messages that mimic legitimate business communications. These aren’t the clumsy, typo-laden scam emails of the past - they’re polished and free of obvious red flags like misspellings or suspicious links.
As AI Journal puts it:
"In a self-managed marketplace, security is no longer simply about protecting data. It is about protecting decisions."
Modern attackers aren’t just after customer data anymore. They’re targeting AI systems and exploiting subtle vulnerabilities to manipulate outcomes. Unfortunately, traditional training programs fail to address these emerging risks, leaving teams unequipped to identify and counter these sophisticated attacks effectively.
How AI-Powered Training Solves Ecommerce Security Problems
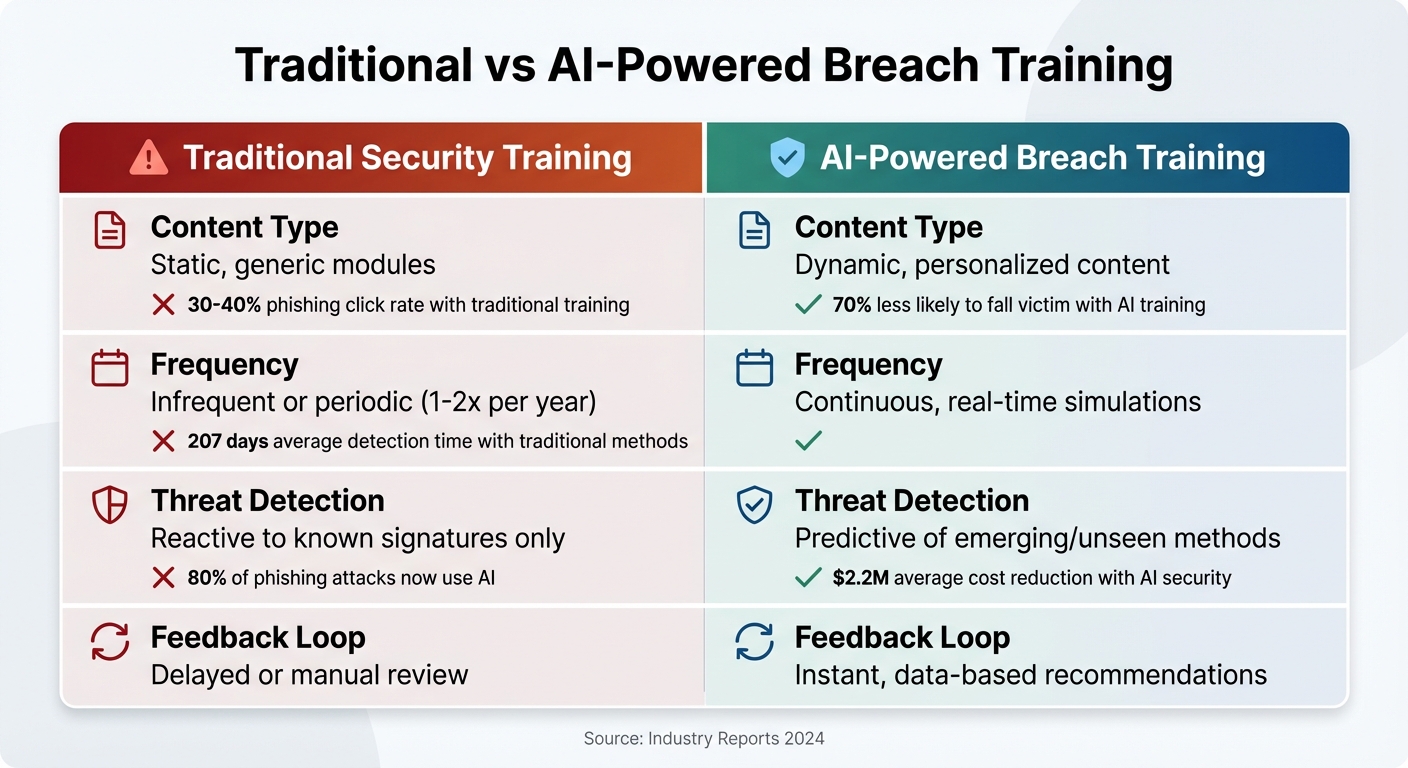
Traditional vs AI-Powered Breach Training Comparison for Ecommerce Security
AI-powered breach simulation brings a fresh approach to tackling ecommerce security challenges. By using real-time threat intelligence and adversarial emulation, these tools create dynamic, evolving scenarios that mimic the full lifecycle of an attack - from reconnaissance to data exfiltration. This shift from static templates to adaptive simulations delivers three major benefits: realistic breach scenarios, customized training, and faster response times.
Creating Accurate Breach Simulations
AI tools excel at crafting breach scenarios that feel authentic and relevant. Using tailored playbooks, they replicate the tactics, techniques, and procedures (TTPs) employed by active threat groups like FIN7 or TA505, which are known for targeting fintech and retail industries. For ecommerce businesses, this means simulations that address specific risks, such as phishing attacks that escalate into privilege abuse and lateral movement across systems.
Rather than focusing on isolated events, AI builds multi-stage "kill chains" to test vulnerabilities throughout an organization's defense structure. Advanced platforms even validate these attack routes with Verified Exploit Paths, ensuring that the simulated vulnerabilities reflect real-world risks. AI red teaming takes this further by targeting ecommerce-specific systems - like fraud detection models - with adversarial prompts. By integrating up-to-the-minute threat intelligence, these simulations ensure teams train against current and emerging attack methods, not outdated ones.
Ongoing and Personalized Training
AI-powered systems move beyond generic, one-size-fits-all training approaches. They adapt continuously to new threats and individual user behavior. As Jericho Security puts it:
"Jericho Security transformed our approach from a generic, one-size-fits-all model to a dynamic, AI-driven solution tailored to our needs."
These systems analyze live data to detect risky behavior patterns in real time, even identifying previously unseen tactics. Generative AI creates evolving breach scenarios, giving teams hands-on experience with realistic phishing attacks. Real-time feedback and predictive modeling help teams not just react to threats but anticipate them. The results speak for themselves: organizations with trained staff are 70% less likely to fall victim to phishing attacks.
AI also uses predictive threat modeling to scan global trends, traffic patterns, and dark web activity, identifying potential attacks before they occur. This continuous learning enables faster decision-making and helps organizations stay agile in a constantly changing threat landscape.
Faster Response Times and Better Decisions
When it comes to responding to threats, speed is everything. AI systems analyze thousands of data points - like geolocation, device type, and transaction patterns - to detect anomalies instantly. This rapid detection reduces the likelihood of successful attacks and minimizes downtime. Adrian Luna from Webscale explains:
"AI reduces the time between detection and response, and fewer successful attacks mean less downtime, stronger conversion rates, and reduced remediation costs."
This efficiency is crucial, especially when 60% of ecommerce traffic comes from automated bots, and global ecommerce fraud losses are projected to reach $44.3 billion in 2024. AI-driven systems help security teams cut through the noise, prioritizing genuine threats and reducing false alarms that lead to alert fatigue. Retailers using AI fraud detection report a 40-50% drop in fraud losses, while AI chatbots now manage 70% of customer interactions from start to finish, giving security teams more time to focus on strategic tasks.
| Feature | Traditional Security Training | AI-Powered Breach Training |
|---|---|---|
| Content Type | Static, generic modules | Dynamic, personalized content |
| Frequency | Infrequent or periodic | Continuous, real-time simulations |
| Threat Detection | Reactive to known signatures | Predictive of emerging/unseen methods |
| Feedback Loop | Delayed or manual review | Instant, data-based recommendations |
Benefits of AI Breach Training for Ecommerce
Early Fraud Detection and Prevention
AI breach training is reshaping how ecommerce businesses identify and counter security threats. By addressing the human factor, which accounts for 68% of all data breaches, these programs focus on training employees to detect sophisticated attacks that traditional systems often miss. On average, AI-driven security solutions lower breach costs by $2.2 million.
One major challenge is that 80% of phishing attacks are now AI-powered, making them incredibly difficult for untrained staff to recognize. Between August 2019 and December 2021, phishing attacks targeting ecommerce platforms caused over $44 million in losses. AI-powered simulations provide employees with hands-on experience in identifying subtle behavioral anomalies and deviations that standard alerts might overlook. This proactive approach significantly reduces the average 207-day detection time, allowing businesses to intercept attackers before they can access sensitive customer data or payment information.
Meeting Data Protection Requirements
AI breach training also helps ecommerce businesses align with stricter data protection regulations. For instance, PCI DSS 4.0, which becomes mandatory in March 2025, requires automated monitoring for compliance with Requirement 6.4.3. This includes enforcing Content-Security-Policy headers and verifying script integrity to guard against Magecart-style attacks. With online payment fraud expected to surpass $48 billion annually by 2026, such automation is no longer optional.
Additionally, the training supports compliance with regulations like GDPR, CCPA, and CPRA by educating teams on how AI systems can discover, classify, and safeguard personal data. A compliance expert summed it up well:
"The integration of AI with unified systems is not merely advantageous; it is indispensable for compliance that is both robust and future-proof." – PieEye POV
For ecommerce companies adopting AI for tasks like pricing and fraud detection, this training ensures teams understand "explainability" requirements. These requirements involve auditing and justifying AI-driven decisions to regulators - a critical capability, especially when 97% of organizations experiencing AI-related security incidents in 2025 lacked proper access controls.
Cost-Effective Security at Scale
AI breach training offers robust security without the hefty price tag of traditional enterprise solutions. For smaller ecommerce businesses, the direct cost of a breach typically falls between $120,000 and $180,000. Beyond these immediate costs, 42% of breached retailers lose more than 10% of their annual revenue due to customer churn within a year. AI training shifts spending from costly emergency responses to manageable, preventive measures.
The scalability of AI solutions is another key advantage. Automated training modules can be deployed across large, remote, or hybrid teams simultaneously - something manual approaches simply can't achieve. As Webscale highlights:
"AI reduces the time between detection and response, and fewer successful attacks mean less downtime, stronger conversion rates, and reduced remediation costs."
This efficiency is critical in a landscape where 60% of all ecommerce traffic comes from automated bots and phishing attacks surged by 250% between January 2021 and May 2022. AI tools also enhance existing security teams by automating repetitive tasks like rule adjustments and reviewing false positives. This allows human experts to focus on strategic priorities rather than sifting through endless logs, making AI breach training an essential component of modern ecommerce security strategies.
Implementing AI Breach Training in Your Ecommerce Business
Using Ecommerce Data to Train AI Models
To make AI models effective in ecommerce, they need to be trained with data specific to your business. As cyber threats become more sophisticated, attackers are using AI to create phishing emails that look like genuine payment processor requests or supplier invoices. To counter this, your AI system must analyze behavioral patterns, device usage, and transaction trends to differentiate between legitimate customers and potential threats. This ensures your team can quickly understand and act on flagged anomalies.
The quality of the data you provide directly impacts how well the AI performs. For instance, research shows that GPT-4's product evaluation accuracy jumps from 16% to 54% when fed accurate, structured data. Similarly, AI trained on outdated or incomplete data may fail to detect subtle warning signs of attacks, such as credential-stuffing or bot-driven inventory scraping. It's also important for your security team to understand why the AI flags certain transactions, as this transparency is essential for both fraud investigations and meeting regulatory requirements. High-quality datasets can also enhance simulated attack scenarios, making training sessions more effective. Once the AI is properly trained, the next step is integrating it into your existing security systems.
Connecting AI Tools with Current Security Systems
To maximize the effectiveness of AI tools, they must integrate seamlessly with your current security framework. This includes connecting AI to systems like Web Application Firewalls (WAFs), Security Information and Event Management (SIEM) systems, and Intrusion Detection Systems (IDS), creating a multi-layered defense. Unlike traditional WAFs that rely on static rules, AI-powered WAFs use behavioral analysis to detect and block zero-day exploits in real time. Deploying AI agents behind API gateways can also strengthen security by enforcing authentication and validating inputs.
Another essential practice is network segmentation. For example, your Cardholder Data Environment (CDE) should be isolated from the rest of your corporate network to limit damage if an AI system is compromised. If you're using autonomous AI agents, consider implementing automatic token rotation every 1–2 hours to reduce the risk of token misuse. As one enterprise security architect put it:
The biggest security risk with AI agents isn't what they're designed to do. It's what they're allowed to do when compromised.
These integrations can significantly reduce response times during a breach, helping to minimize the overall impact. With these systems in place, the next priority is tracking their performance.
Tracking Performance with Key Metrics
Monitoring specific metrics is essential to measure the success of your AI-driven security efforts. Start by focusing on Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) - ideally, detection should happen in under 5 minutes, with a response time of less than 15 minutes. Another critical metric is the false positive rate; aim to keep it below 5% to avoid overwhelming your team with unnecessary alerts. AI systems can reduce false positives by as much as 70% to 80% compared to traditional methods.
| Metric Category | Specific KPI | Target Outcome |
|---|---|---|
| Response Speed | Time to Mitigation | < 5 minutes for detection |
| Accuracy | False Positive Rate | < 5% to reduce noise |
| Fraud Prevention | False Decline Rate | Improved approval accuracy |
| Compliance | Patch Compliance Rate | Real-time/Automated |
Another metric to watch is dwell time, or the time between a breach occurring and its detection. The industry average is 207 days, but your goal should be to reduce this significantly. For ecommerce businesses, monitoring the false decline rate is also crucial to ensure legitimate transactions aren't mistakenly blocked. Adrian Luna from Webscale highlights the broader benefits of AI:
AI reduces the time between detection and response, and fewer successful attacks mean less downtime, stronger conversion rates, and reduced remediation costs.
Conclusion
AI breach training is more than just a defensive measure - it's a smart investment in protecting your revenue, customer data, and competitive edge. With global ecommerce fraud losses forecasted to hit $107 billion by 2029 and over 65% of online retailers likely to face at least one major breach by 2026, the stakes couldn't be higher.
Consider this: 74% of all data breaches involve a human factor, and up to 80% of phishing attacks are now AI-powered. By equipping employees to spot and counter these increasingly sophisticated threats, you turn your workforce from a potential weak link into a "cyber shield". This proactive approach doesn't just lower the chances of expensive breaches - it also helps you avoid hefty regulatory fines.
But the benefits go beyond immediate risk reduction. AI breach training builds customer confidence, a key ingredient for sustainable growth. As Aleksey Gureiev, Technical Lead at Shakuro, puts it:
In a marketplace where AI capabilities are rapidly becoming standard, responsible development is the true differentiator.
Visible security measures - like real-time fraud alerts and biometric authentication - send a clear message to customers: their data is safe. This reassurance fosters loyalty and increases lifetime value, giving you a competitive edge.
Operationally, the advantages are hard to ignore. AI-driven security tools offer real-time monitoring and predictive risk analysis, allowing your team to focus on growth instead of constantly putting out fires. With the global average cost of a data breach sitting at $4.4 million, investing in AI breach training pays off by preventing problems before they spiral. Companies that make AI security a priority at the highest levels show not just preparedness but also long-term vision, setting themselves up for success in an increasingly complex digital world.
FAQs
What is AI breach training in ecommerce?
AI breach training in e-commerce leverages AI-driven simulations of cyberattacks to help businesses prepare for potential security threats. These simulations focus on identifying vulnerabilities in key AI-powered systems, such as pricing algorithms, fraud detection tools, and inventory management platforms. By exposing these weak points, companies can strengthen their defenses and enhance their ability to respond to real-world threats.
This forward-thinking strategy plays a crucial role in safeguarding AI systems, which are becoming increasingly vital to e-commerce operations. In doing so, businesses not only protect sensitive data but also maintain the trust of their customers in an ever-changing cybersecurity environment.
How do I integrate AI breach training with my WAF and SIEM?
To make the most of AI breach training with your Web Application Firewall (WAF) and Security Information and Event Management (SIEM) systems, follow these steps:
- Set up your WAF and SIEM: Make sure both systems are properly configured to detect, log, and analyze security events effectively. They form the backbone of your monitoring and response efforts.
- Leverage AI-driven breach simulations: Use AI tools to simulate potential breaches. These simulations help uncover vulnerabilities and provide hands-on training for your team, sharpening their skills.
- Centralize alerts with SIEM: Integrate AI alerts into your SIEM using APIs or syslog. This ensures all security data is monitored in one place, making it easier to spot patterns and respond quickly.
- Keep scenarios up-to-date: Continuously refresh your training scenarios to reflect the latest threats. This helps your team stay prepared and improves your response strategies over time.
By combining AI insights with your WAF and SIEM, you'll create a stronger, more adaptive security framework.
What metrics prove AI breach training is working?
Metrics like chatbot resolution rates (e.g., 71%) and data quality indicators - including accuracy, completeness, and timeliness - highlight how well AI training performs in ecommerce. These numbers provide a clear picture of how effectively AI systems manage tasks while ensuring data remains dependable.





